Cybersecurity Assessment
Discover your security gaps to improve your business risk posture.
Get a comprehensive cybersecurity risk assessment with our proprietary AI Security assessment platform. 30-day turnaround, board-ready insights.
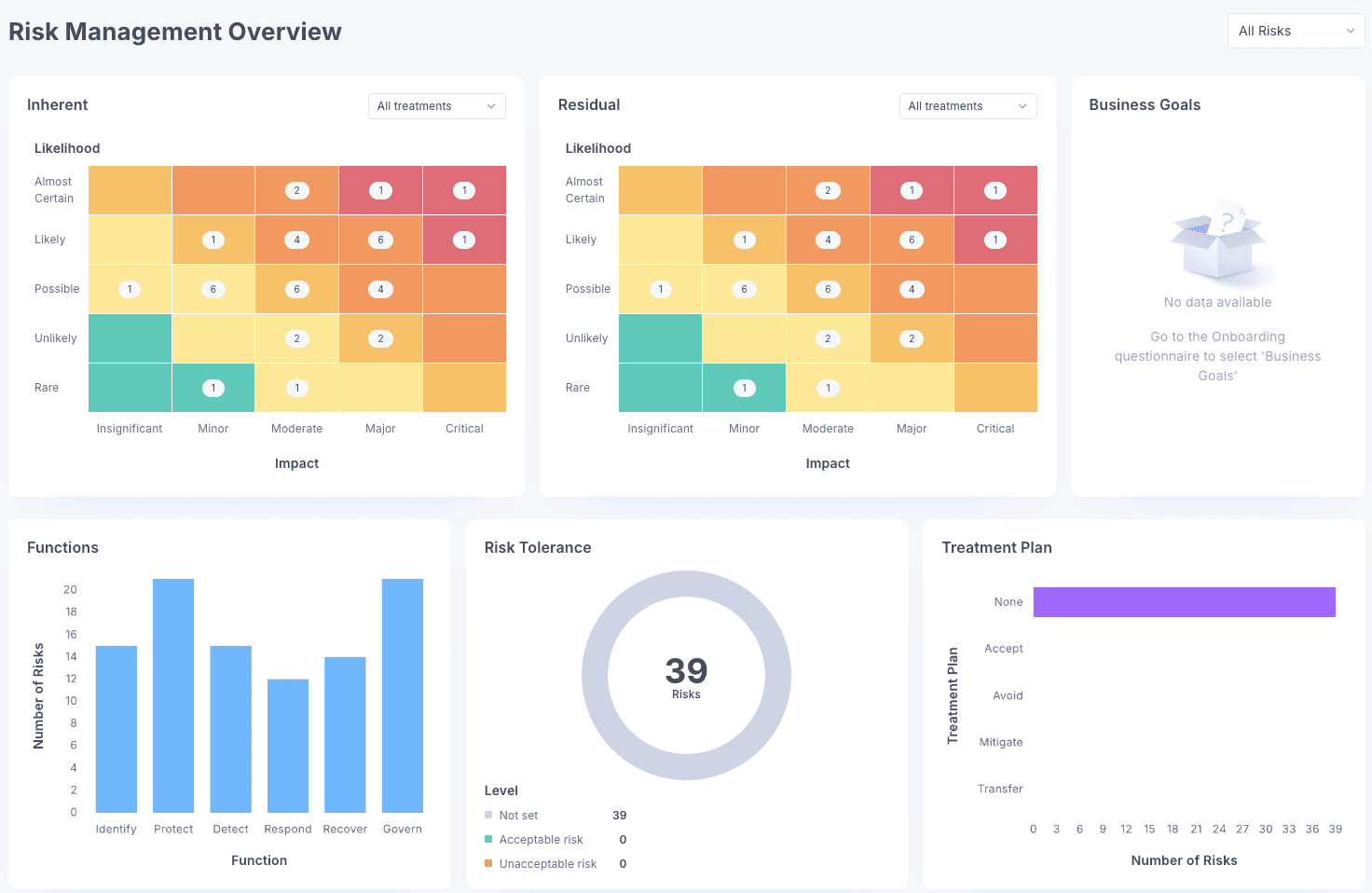
Picture Your Risk
Stop guessing. Get an evaluation of your security posture against leading frameworks.
Critical Gaps
Understand which issues are high-risk versus low-impact.
Industry Benchmarking
Know how your security posture stacks up against similar companies.
Prioritized Fixes
Get a step-by-step plan on what to fix first for maximum risk reduction.
No more guesswork. Get a clear roadmap.
Built on our experience protecting high value targets.
What You Get
01. AI-Powered Assessment Platform
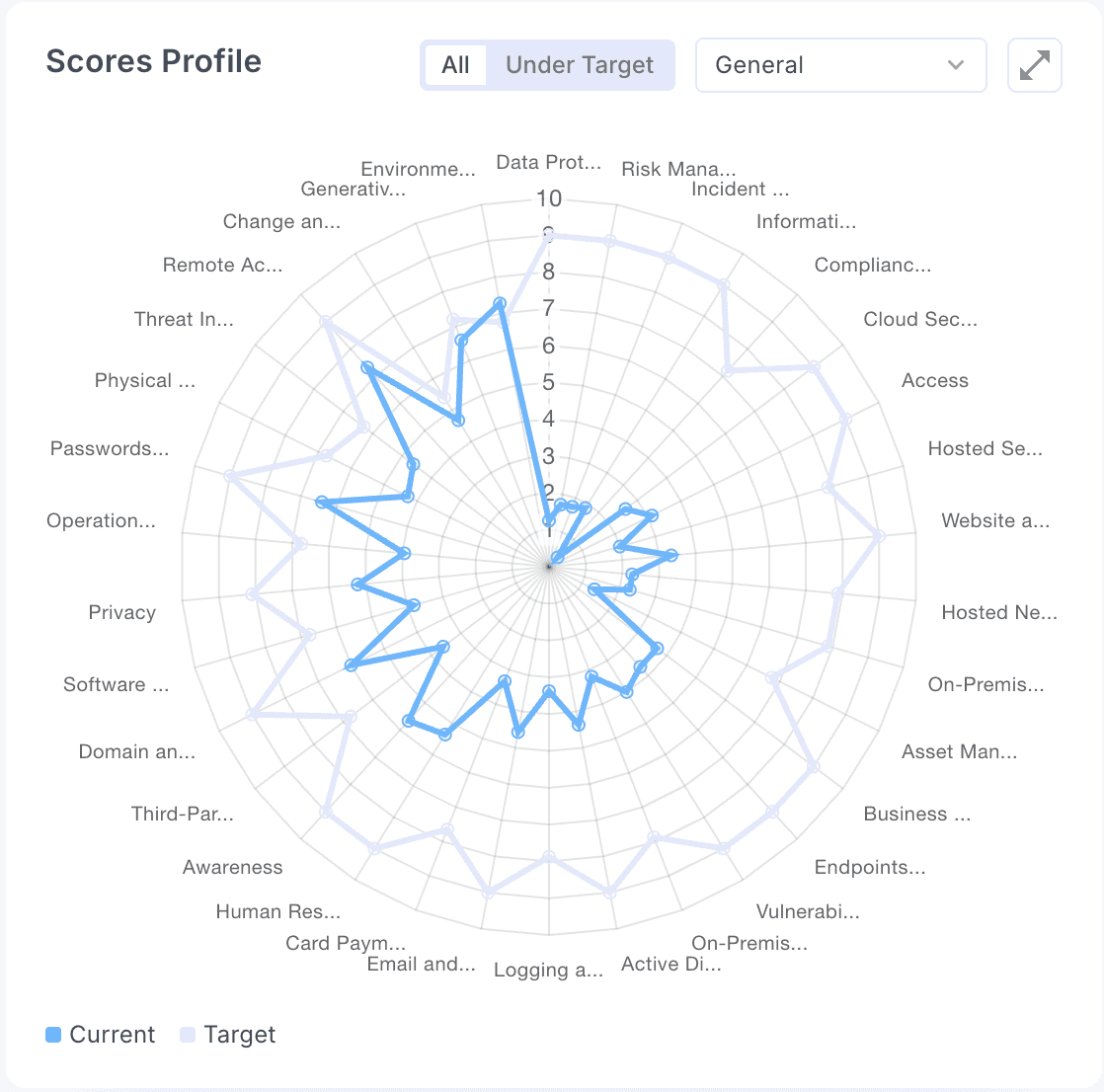
Visibility into your entire security posture.
- Guided self-assessment workflows
- Real-time risk scoring across domains
- Policy gap analysis (NIST, ISO, SOC 2, HIPAA, GDPR)
- Task assignment + priority tracking
- Visual risk mapping (spider + maturity charts)
- Automated evidence collection for audits
02. Full Technical Report
A deep, audit-ready analysis of every domain, gap, and risk.
- Security posture across governance, access control, IR, BC, etc.
- Detailed policy + control gaps
- Compliance mapping to major frameworks
- Assigned tasks with owners + deadlines
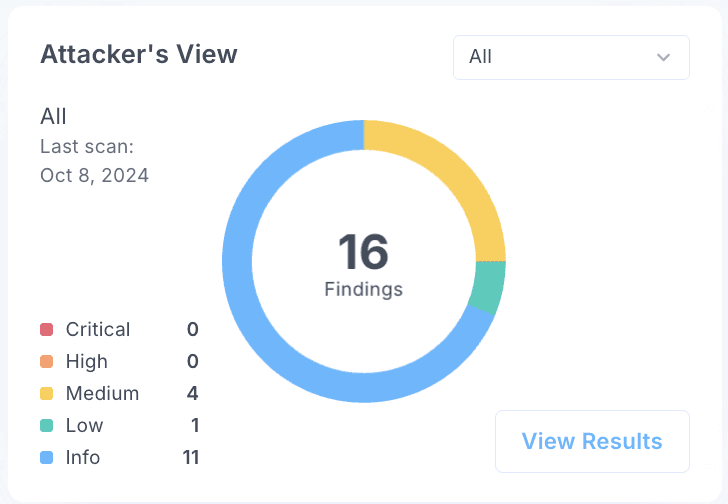
- Vulnerability insights tied to risk posture
03. Prioritized Roadmap
A step-by-step plan your team can execute without confusion.
- What to fix first, second, and third
- Task ownership per team/role
- Re-assessment schedule to measure maturity
04. Executive Summary
Board-ready insights that translate technical findings into business impact.
- Clear risk visuals for leadership
- Top 5 Risks
- Budget recommendations
- Non-technical next steps

How It Works
Discovery
We meet with your team and review your current environment, policies, and controls.
AI-Powered Assessment
We work together to complete a self-assessment using our platform. We analyze results, review documentation, and identify gaps.
Reporting & Roadmap
We deliver your technical report and executive summary, then walk you through findings and answer questions.
What Happens Next?
Most clients engage us for ongoing fractional vCSO services to oversee remediation. But if you just want the assessment, you own the report and roadmap.
Who This Is For
Built for companies that need clarity, not confusion.
Preparing for SOC 2, ISO 27001, or audit reviews and need to know where you stand.
You’ve outgrown ad-hoc security and need a structured evaluation before your next raise or enterprise deal.
Banking, healthcare, fintech — you need a security baseline that satisfies regulators and auditors.
You know something’s missing but need an experienced eye to pinpoint what and how to fix it.
Leadership You Can Trust
Expertise You Can Measure
vCSO.ai was founded by Nick Shevelyov, cybersecurity executive, speaker, and author of Cyber War and Peace.
With over three decades of experience advising Fortune 500 companies, boards, and government agencies, Nick bridges technology, governance, and business strategy to help organizations thrive securely.

Achievements
25+ years in cybersecurity, risk management, and leadership.
15 years as CSO for Silicon Valley Bank (2007–2021), the bank of the innovation economy.
Deep network across cybersecurity, venture capital, and startup ecosystems.
Recognized speaker, advisor, and thought leader in cybersecurity governance.
Author: "Cyber War…and Peace"
Assessment Team
Every assessment is customized to your business, industry, and risk profile.

Andrej
CISSP, ethical hacker

Berk
GRC specialist fluent in NIST, ISO, SOC 2, HIPAA, FFIEC
Supported Frameworks
We align your assessment with the framework most relevant to your business.
NIST Cybersecurity Framework (CSF)
General risk management, mid-sized companies
ISO 27001
International clients or certification seekers
SOC 2 Type I/II
SaaS companies, cloud service providers
HIPAA Security Rule
Healthcare providers, health tech
FFIEC CAT
Banks, credit unions, financial institutions
GDPR
Companies with European customers
Custom Framework
Unique compliance or industry-specific requirements
What Happens After the Assessment
01.
Take It and Run
You own the report and roadmap. Implement internally with your team.
02.
Ongoing Fractional CSO
Most clients engage us to oversee remediation, track progress, and re-assess quarterly.
03.
Audit Preparation
We help you close gaps, gather evidence, and prepare for third-party auditors.
FAQ
Common Questions
How long does assessment take?
30 days from kickoff to final report delivery.
Do we need to pause operations?
No. Our assessment integrates into your normal workflow. We work alongside your team without disruption.
What if we find critical vulnerabilities?
We flag them immediately with a recommended remediation path so you can act fast.
Can you do penetration testing too?
Yes. We can include penetration testing as part of or alongside the assessment engagement.
Is this enough to pass SOC 2 audit?
The assessment identifies gaps against SOC 2. We then help you close them and prepare for the audit.